
Fancy a high-profile cybersecurity job? Here’s one for you.
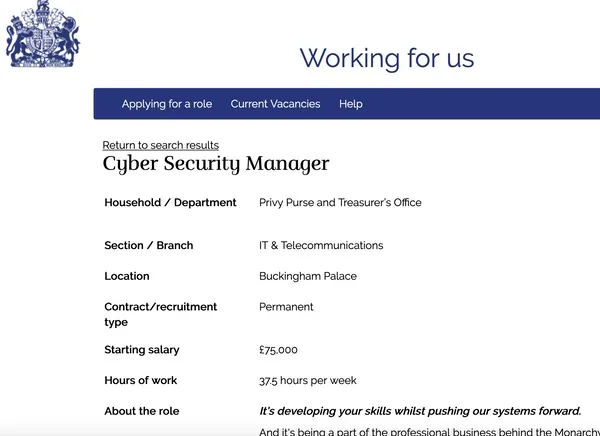
Role: Cyber Security Manager.
Location: Buckingham Palace.
Yes, the Royal Household is advertising for a cybersecurity expert to head-up its team digitally defending King Charles, his family, and their workers.
Reporting to the Director of Digital Services, the successful candidate will find a fair amount on their plate:
- Leading the maturity of the Cyber Risk Management strategy and the Cyber security framework delivery in line with best practice.
- Leading an in-house team to take action to reduce cyber risk and build resilience against cyber-attacks.
- Working with the Enterprise Architecture team to mature a secure by design culture.
- Evaluating, reviewing, and advising on best practice, drawing on external expertise, including the National Cyber Security Centre (NCSC).
- As subject matter expert, building understanding and upskill the wider Digital Services Team and other key stakeholders
- Encouraging a cybersecurity culture and awareness so that all employees understand the role they play.
- Working closely with information security colleagues to support compliance.
Yeah yeah yeah, but let’s cut to the chase – what’s the money like?
Starting salary; £75,000
Hours of work: 37.5 hours per week
Hmm.. that’s certainly not the most generous salary in the world for a role with that kind of responsibility, especially when you consider the cost of living in London. (I’m guessing King Charles isn’t offering his spare bedroom)
Mind you, the Royal Family has long had a reputation for not paying its lackeys the highest salaries.
But don’t worry, you will have the prestige of working for a man worth an estimated £1.8 billion!
And if that’s enough to convince you, just check out some of the perks of the job…
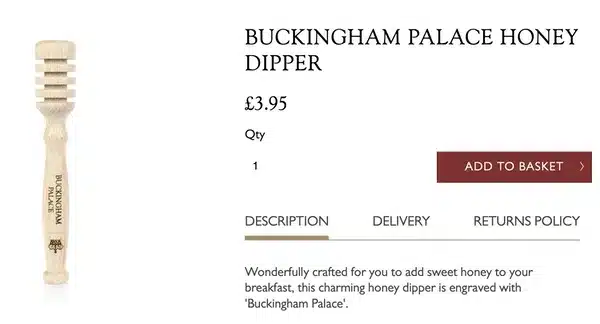
Other perks include 20% off at our Royal Collection Trust Shops and complimentary admission tickets across all our locations, along with many more exclusive employee discounts.
Oh great! I’ll be able to spend some of my money on a cut-price Buckingham Palace honey dipper, tea cosy, and a porcelain trowel! What a treat!
There is no doubt that the Royal Family is a target for hackers. Not only have some members of the British press shown they are prepared to break the law to gather information about the Royals, but we’ve also seen recent cyber attacks against the Royal Family’s website.
To hear a discussion of the distributed denial-of-service (DDoS) attack against the Royal Family’s website, listen to this episode of the “Smashing Security” podcast.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
You know, Graham, I've got to take you to task here because you have an issue with people like Piers Morgan, which, you know, I can sympathise with.
I'd run him over, right? But Thom—
Hanks has done nothing to you. You can just avoid him. He's done nothing. He's just a nice guy. Is he a nice guy? Maybe that's what threatens you.
Is he? I don't know.
Smashing Security, episode 342 Royal Family Attack, Keyless Car Theft and a deepfake Thom Hanks with Carole Theriault and Graham Cluley.
Hello, hello and welcome to Smashing Security, episode 342. My name's Graham Cluley. And I'm Carole Theriault. And Carole, we are joined this week by a special guest someone who's been on the show many, many, many, many, many times before. It is, of course, the one, the only Maria Varmazis.
Hi. I'm glad you had to say it in an approximate Greek accent, I think. That was very nice. I liked it. Hi, yes, hi, everybody. Welcome back. It's been a while. Yes. Welcome back. Thank you. The badass space bitch has returned. Do you have a t-shirt with that? No, I should, though. I really should. I like that. That feels right.
Not just a space bitch, but also you, well, both of you actually have been pickling some stickies lately, haven't you? That's your other podcast is back in town.
Yeah. Sticky flipping pickles, sticky pickles. Just in case people are trying to Google what it is. It's called sticky pickles. It is back. It is back. It is back. Definitely. And it's great fun. So—
It's not security related necessarily. Definitely. Better not—
Be sticky pickles. Although, should we kick this show off, people? Actually, first, maybe we should thank this week's wonderful sponsors, Gigamon, Devo, and Hunters. It's their support that helped us give you this show for free. Now, coming up in today's show, Graham, what do you got?
I'm going to be going deep, deep into threat actors. Oh, okay. What about you, Maria?
A PSA on car hacking. A PSA on car hacking. I don't know what that means. And I'll be looking at a royal mess. Plus, we have a featured interview with Devo's very own CISO. I love how that sounds. Kayla Williams. And we're going to talk about all things SOC with security analytics platform Devo. All this and much more coming up on this episode of Smashing Security.
Now, chums, chums, what is the worst Christmas movie of all time, in your humble opinion? The worst. The worst. You don't—
Really remember the worst. Oh, I do. There are a lot of bad ones. Okay, come on, name one, name one, name one. I was going to say The Snowman, but I actually really love that film. Yeah, I like The Snowman. I think if there were anything with the chipmunks, I would not be a fan. Yeah, anything chipmunks, yeah, agreed. Wasn't—
There a Star Wars holiday special as well or something?
One doesn't talk about the Star Wars holiday special. No, we don't talk about it.
The actual answer is the Polar Express.
Oh, stop. Oh, no, no, no. I'm with you on that, actually. Why? That movie's awful. Guys, I've seen it. It was all right. Well, was it all right? Was it all right? Everybody's kind of rubbery and Gumby-like. Yes,—
Exactly. Maria, absolutely correct. Came out in 2004, directed by Robert Zemeckis, who also did the Back to the Future movie, which we like. Yeah. Yeah. Polar Express. Polar Express was this computer animated fantasy movie about this kid making a magical train journey to the North Pole to meet Father Christmas. And what makes it bad is the uncanny valley. It's a grotesque horror, is the reality about the Polar Express, because you're going to give kids nightmares if they want. In fact, as an adult, it's going to give you the creeps because you're watching this dead-eyed animated train conductor with the voice of Thom Hanks. Yeah, yeah. And it's creepy. It's creepy.
I have seen this. I don't remember it. I wouldn't say it's a great film or anything like that. Your mind blocked it out. The trauma just said no.
It is traumatic. Thom Hanks, he earned $40 million. That's all? No, it wasn't all. He earned $40 million for providing the voice of various characters in the movie. And he also said, you know what? I want an extra 20% of the gross takings. Smart man. In all. I think this is the way he often does it, actually. He takes a lump sum, but also gets some more as well if it's a success.
Thom, you may want to come on Smashing Security because we get paid a lot better than that over here. Oh, yeah. A lot of money. Easy piece.
Easy piece. Yep. He earned, in total, over $100 million for that movie. And there's been plenty of other movies where he's done the same as well. Man, that movie. Just for doing a bit of voice work. Just for, you know, doing a bit. And—
He's kind of shouty in the movie, too. Is that my imagination? I remember him being shouty. I can't watch it. And I was sort of like, yo, Thom Hanks, just back off. I was just going to say, Graham did not research the story properly by watching the film. I assure you of that. I have seen—
Part of the movie before. Then I realized it was Thom Hanks and turned it off. And that's my general approach. You have—
A Thom, yeah. I've got a Thom problem. You're not a fan of Thom Hanks, of America's Uncle. No, I'm not a fan of Thom Hanks, no. Oh, my goodness. I have a problem. I have some kind of problem, frankly, when it comes to Thom Hanks. There's something which just simply stops. And also, you know, deportment, deportment. You look the most of Thom Hanks of the three of us.
How dare you? There's something about Thom Hanks. I'm sorry if there are any Thom Hanks fans out there.
Yeah, there's going to be one in the thousands and thousands of listeners we have. There's not one.
There's something about him. I don't want to encourage violence, especially against someone who some people would. Wow, shit just got real. All right. Anyway, Thom Hanks has just warned his nine and a half million Instagram followers. Who's doing that? Who's following Thom Hanks on Instagram? I'm sure loads of people are.
People follow you, don't they? Apparently 9.5 million people are. How many do you have on Instagram?
Not as many as 9.5 million. It's very generous. It's comparable. Thom Hanks has told everyone, he says, you may have seen an advert which is using my face, but it's not me who's promoting this dental plan, he says. There's a video out there promoting some kind of dental plan, he says. They are using an AI version of me. And he says, I've got nothing to do with it. He does have nice chompers, though. He'd probably been getting 20% of the proceeds, I expect. That's what he's grumpy about. Anyway, so Thom Hanks, despite appearing in the Polar Express and ruining many children's Christmas and some adults as well. He's got an issue of this, and it's not the first time he's had a bit of a whinge about the wonder of artificial intelligence. Earlier this year, he was on the Adam Buxton podcast. I quite like Adam Buxton. I don't know why he invited Thom Hanks on. But anyway, he was on the Adam Buxton podcast, and he said that AI could be used to extend the careers of actors. Here's what Thom Hanks said. I can't do a Thom Hanks impression. Thank God.
You could use AI for this, though. Yeah, you need some acting skills to be able to do that.
Anybody can now recreate themselves at any age they are by way of AI or deepfake technology, he said. I could be hit by a bus tomorrow, and that's it. But performances can go on and on and on and on. And I thought...
That's not exactly an endorsement of AI. No, I don't think it was meant as one.
I thought that was a terrible thought, the thought that his performances could go on and on and on and on, even if I do get a job as a bus driver and one day run him over.
You know, Graham, I've got to take you to task here because you have an issue with people like Piers Morgan, which, you know, I can sympathize with.
I'd run him over.
Right? But Thom Hanks has done nothing to you. You can just avoid him. He's done nothing. He's just a nice guy. And maybe that's what threatens you.
Is he a nice guy? Is he? I don't know. It's a bit like saying his are a nice guy. I don't know. I'm not sure. Is she or isn't she? I don't know. In this kind of new reality we live in, I just don't know what to believe anymore. All I know...
He's a deepfake all the way down. So his fakery goes deep is what I'm saying, because I saw his Oscar acceptance speech all those years ago when he gets all emotional, a bit like Gwyneth Paltrow. And I think, oh, come on, this is just too... That cheery, cheery movie about AIDS.
Don't make me feel bad because it was a worthy movie.
I think you just need to step off a little bit. It's just a little bit too cray cray.
Let's move on from Thom Hanks. Let's do that. To Robin Williams. Now...
You better not have a problem with Robin Williams. Just saying. Okay, look, listen. Zelda Williams, who's the daughter of Robin Williams, she's posted on Instagram in the last week that deepfakes are, at their very best, a poor facsimile of greater people. And she says, at worst, they are a horrendous Frankensteinian monster. I think she could just say Frankenstein monster cobbled together from the worst bits of everything in this industry is. Can you leave him alone? Well, no. He was funnier than you. I'm sorry. Everybody has flops. It happens. So there's lots of stars, as we know, who are getting upset about the use of AI and deepfakery. Last month, there were reports. I think the Telegraph reported that Bruce Willis had sold his face. Not like Nicolas Cage and John Travolta swapped faces. Face off. And that's really hard because he's not well, right?
Well, it's not well. Anyway, it's been denied. Apparently, Bruce hasn't sold his face. So that's good. But he has recently done an advert with Deep Cake, which uses a deep fake for him for a Russian telecoms company. So he is doing a bit of acting, as it were, without actually having to do anything because they're just using the... James Earl Jones, the great James Earl Jones.
We like this guy. Okay.
We like him because he did Darth Vader's voice. Yes. Apparently he's retired now, but they're using tech to keep doing Vader's voice alive and making him sound younger because he obviously is. Did you see him in that episode of The Big Bang Theory, James Earl Jones? No. Okay. Didn't miss much. So what's clear is that actors really care about this, right? Thom Hanks, who's the governor, he's the godfather. He cares about this. And the current Screen Actors Guild strike that is in part, not entirely, but in part about the dangers of new technologies like AI, digital recreation, leaving them out of pocket. And I have sympathy for that. I have sympathy for that because all of us potentially, if there were, for instance, 342 hours worth of me just prattling away into a microphone, or maybe you, Carole, as well. I don't prattle. Who would listen to that, though? Honestly. Who would? They could potentially create new content and that could be used to, you know, make all kinds of money for dental plans and things like this. What sucks? So I wonder. Can I just say so I can just interrupt for a sec? And that means the media are then going to write about it, if you're famous, like Thom Hanks. And you then cover it on the show. Yeah. Exactly. And people will replay that, I don't know, fake dental ad or whatever it is that uses the AI, giving that particular promotion even more oxygen.
Right. It's the Streisand effect. Thank you very much, Graham.
No one could fake. No one could fake Barbara Streisand.
I'm sure someone has tried. I love Barbara. You hate Thom, but you love Barbara. Okay. I mean, Barbara's great. Don't get me wrong. But yeah, it's a consent issue, is it not? I mean, really. Don't you own your face? Yeah, I mean, yeah, right. It's just a basic thing. If you say it's okay for you to do it for this one instance, then fine. But if you do it without the other person's permission, you're just stealing someone's essence. I mean, you're putting words in their mouth. Literally, you're making their fake mouth say the fake words. Who wants that? Nobody. I mean, that's just creepy. You got your AI hand up their butt and making them spout out garbage like a little puppet. That's what you're doing. It sucks. Beyond the Black Mirror episode. My God, it's creepy beyond all hell. It's gross.
So I'm not sure what the answer is to this, but obviously AI and deep fakes, lots of people are talking about it. So there will be technology companies who are now claiming that they've got the solution. I've seen companies saying what we need to do is proactively tag real, genuine content. Yeah. Probably involving the blockchain I'm guessing as well they'll introduce that in some way.
Oh boy that's okay yep.
Or maybe that the things which generate deepfake they could embed some sort of signature but again people are going to get around this I can't see how this is going to simply detecting it after the fact isn't going to be strong enough because deepfakes are going to get more and more convincing and I know some chip
Makers are working on that, having real-time deepfake and AI video detection capabilities. It's a thing that many of them are trying to do for this reason. But I'm just thinking, I'm going to flip the coin because I completely understand why the actors don't want this and I wouldn't want it either. I'm thinking of a situation where there's this podcast I listen to sometimes called Dudesy, where it's two comedians, I'm not going to bother naming them because either you know or you don't, that use AI and they're very explicit about the fact that they are using AI to write these crazy episodes that they are sort of reacting to. And they actually had AI Thom Hanks, video and audio of AI Thom Hanks saying this crazy pitch for a fake movie, Ghost Train or something really ridiculous. And it's hilarious because it's obviously a fake version of Thom Hanks. They're very upfront about the fact hey, this is fake, this is not real this is AI and for that it's really funny. But if it was my face being used without my consent to do something super funny in my voice that I didn't we would be able
To detect it was a deep fake in your case if it was being really funny wow I think
I know and I'm in the same camp. I think it's Thom Hanks at the moment, yeah, he's so famous. People have been doing this since before AI, you know, impressions and granted, he got 40 million, right, for a job that I'm sure is easier than you know, packing fruit every day for 12 hours every day. So those are your only options? No, I'm just saying it's a lot of money. Don't you think it's a sexy amount of change for the work? Does that mean we own him completely? That's correct? No, yeah, no, no, definitely not. So yeah, it is a consent thing in the end. But I'm just thinking of that random podcast from like they are making sure everyone knows that it's fake, but it is an AI version of him. So I don't know, does that make it okay?
I want to know what dental company chooses Thom Hanks?
It's got great gnashers. We talked about the best Hollywood can buy. See, this Instagram thing, it looks like him from 30 years ago though.
Oh yeah, they de-aged him as well. They de-aged him. That's almost weirder.
It's like where did this come from? And I love that he has to go, "Hey guys, that's not me, by the way. I didn't record this dental plan ad when the internet didn't exist."
Maria, what's your story for us this week?
Well, mine is a bit of a PSA or a public service announcement for our listeners today about a thing that I didn't really know existed or didn't take terribly seriously. So I'll sort of walk you through my thought process on this. So what do you both think of when you hear the phrase "car hacking"?
Oh, normally I imagine Charlie Miller maybe hacking into a vehicle as it goes down the highway and hijacking its radio or its steering or something like that. Something a little bit James Bond, something like that.
Yes, yeah, something maybe with Wi-Fi or something like that. What about you, Kroll? Yeah, no, I don't know a lot because I have an old car, right? So I just don't really know a lot about
Modern fangled stuff. Kroll's got an old car, so it's got a crank at the front and a man running in front of it with a red flag and
Every 30 feet you have to get out and recrank it. Oh no. When I was hearing the phrase "car hacking," I was thinking it was something basically Wi-Fi enabled cars or Graham, sort of along the lines of what you were saying. But I saw something on X, formerly known as Twitter, and it showed a video of a car being stolen from someone's driveway and it took just moments. And I was sort of like, what the heck is going on here? So I wanted to read up about it. So basically, that one form of car hacking that's really on the rise has been over the past few years, it involves keyless entry systems. So those little key fobs, and Kroll, you sort of mentioned this, so since you don't have a newer car, I don't know if you know how these work.
No, no, explain it to me. Explain it to I'm going to lady-splain it a little bit. So the new keyless entry systems that cars have, where you basically don't need to take your key out of your pocket or your purse or whatever, you just walk up to your car, press a little button, and the car unlocks just by being in proximity to your car with the key. Are you there? Are you there? Are you there?
Yeah, essentially, yeah, they're checking for each other all the time. So okay, second question for you both: where do you keep your car keys?
Well, I need my car keys in order to start the car because I want to steal them right away, right? That's how old school I am.
Right?
So Maria, I haven't had my car stolen like this. My ex-wife has had her car stolen through this method.
Oh my God.
And as a result, I keep my car keys in a little box, which is basically a Faraday cage. It doesn't allow the device to communicate with the outside world because this is a genuine, really serious problem. So I always put my car keys in one of those.
I didn't know this was a thing. And so essentially, so I'm going to be telling you stuff that you already know, but maybe our listeners don't know.
That's right, I'll act dumb. I'll pretend they don't. Pretend
You didn't know about any of this. Yeah, this is keyless car theft or relay attacks is apparently the more formal name. There's a couple different names for this. It's becoming very popular way to steal cars. And apparently in the UK, it's especially popular. So I was noticing that when I was doing the research on this. Seems in the UK, this is happening a lot. The UK National Police Chiefs Council says it's been on the rise last several years. They've been doing a lot of studies about it. Less is known in the US. Essentially, the car manufacturers know it's a thing. But I don't think anyone's tracking it aside from AAA, but I couldn't find any numbers. Maybe listeners will find it. But essentially, if you keep your car keys on a hook near your front door, or maybe on a hook near your garage, or on a table near a door, or an external wall, that can sort of be a way for a car thief to hijack the signal. It's an easy way for them to hijack the signal because the key is so close to where they are standing. So let me walk you through how the attack actually works. It's kind of fun to look at. Not so fun to be the receiving end of it. They use this thing called a frame antenna and it's super basic. It looks kind of like a square coat hanger. And the criminal stands outside your front door where they think your key is. In many cases, it's a good bet. And they nab the signal from the car key fob that's continuously talking to the car. And then they've got a second friend who's standing near the car holding a portable device, and then that second friend can then receive the signal from the first guy, unlock the car, and then use that device to start the ignition and drive the car away. That's exactly it. Yeah. So there's no smashed glass left on your driveway the next morning. There's no car alarms to go off. All you know when you wake up next morning is your keys are exactly where you left them. You had definitely locked your car, but your car is just gone. And then everyone's like, did you really lock your car? Are you sure? And you're like, I'm 100% sure. Yep. And you call the police and they ask you that question and they're like, well, there's no evidence of a crime or whatever. And you're just, what the hell is going on here? Right, Graham? That's how you guys felt, I'm guessing.
Yeah, it didn't happen on my watch, can I stress. So it happened to my ex-wife. But obviously, she was very shocked by what happened. And it is so easy to do. And it is very common, at least here in the UK it is. And people are typically stealing cars to order or high value cars so she has quite an expensive car which is what they stole and it is as though someone has walked up to a car with the keys in their pocket because it's relaying the signal from the key which is still inside your house when it happens and that's why I keep my key in one of these little special boxes to prevent it from working.
You can buy them online or you can buy them at shops and you can test that they actually work because you can put your keys inside the box, then walk up to your car with the box. And if your car won't open until you open the box, then you know that the box works.
That's a very good way to test it.
Yeah, because apparently earlier this year on everyone's favourite social media channel, TikTok, there was a viral car theft challenge. Oh my goodness. Teaching people how to actually steal cars with this relay attack method. And if you want to buy the kit online for basically the frame antenna, it's 80 pounds, 100 bucks. Right. So not expensive. And the range that these antenna can usually pick up the key fobs from is like five to 20 meters. So it's actually that's more than I would have thought. So I was thinking even if your key is not by the front door. Yeah, it's 60 feet. Yeah, your keys can be pretty far into your house and they could potentially find the signal. And the UK car security company Tracker said 92% of cars that recovered last year were taken without using the keys. So I'm not saying it's all with this attack, but this is the problem with this country because very few villages have driveways, right? Their houses are right on the roads with a tiny front garden. So no wonder it's rife here. In the States, at least, a lot of people live in the, have a bit of front lawn to give them some distance. Well, people just walk up to people's cars and driveways even in the US. I've seen videos of it here. They'll just walk up at night when people are sleeping.
I think the real problem here is the car companies. Because why do we have this keyless entry to vehicles? Why, when I walk up to my car, if I've got my keys in my pocket, why does my car start to unlock and expect me just to press a button? Why isn't it that I have to press a button on the actual key for it to send the signal to communicate with the car to unlock it?
Well, that's how it worked when my car was alive and remains alive.
Yeah, yeah, yeah. With your car, absolutely. Absolutely. But what they've done is they've introduced this feature and there's no way to turn the bloody thing off because I, for security reasons, would like to turn that off in my car so that I don't have keyless entry. I want to have to press the button or something. They have no other option. They don't have a dumb option. And for several years now, because apparently this started really becoming an issue at the beginning of the pandemic and it's only gotten worse. Apparently, several trade groups have written to the car manufacturers and they've responded, the manufacturers saying, we're aware of the issue and haven't really promised any action necessarily. Although, as far as I know, Ford has said that its newer models are going to have the option to put the car into sleep mode. That's not dumb actually. It's not. I'm just, I would never, I would forget they're in there and I'd be, it's next to the lettuce. Yeah, cold keys, everybody's favorite, especially winter.
My favorite is put it in a cookie tin, a little metal cookie tin, which historically was what grandmothers would put sewing supplies in. So I'm just imagining kids looking at the cookie tin and going, oh, there's cookies. And instead of being sewing supplies.
Yeah, it's an old dictionary. You could dig out the metal. You can do that. Is that going to stop? No, probably not. I mean, that's the thing.
Whatever you choose, you've got to test that it properly works. Yep. And also you've got to make it easy enough that you don't have to always remember, oh, got to get some more tin foil and wrap it up because you won't.
You definitely won't. So I think just buy yourself a little box and put it somewhere convenient and just make it a habit of always putting your key in there.
Good advice. Yeah, they sell Faraday pouches or wallets that you can use, so they're available. But you can also just keep, if you have a larger property, I suppose you could keep your car keys away from a front door, especially if your front door is near your car. I don't know if that will actually help, but that is an option.
Let the air out of your tires, maybe. There'd be another suggestion.
I've actually read suggestions of literally putting a metal boot on your car when you park it.
Oh, clamp it. Yeah, literally just make it impossible to drive. Not inconvenient at all.
Not inconvenient. I used to have a wheel clamp, a steering wheel clamp. It was a massive thing.
Oh, the club. Yeah. And I had kind of a little fast nippy car for a little while. And yeah, anyway, it was a pain in the ass to use, but no one stole it.
I did use it all the time. I also had a club in the 90s. I drove a little shit box and that was the only way it never got stolen. Yep, yep. Well, FYI for listeners, I didn't know about any of this so and I hope it helps somebody not get their car stolen. Great story, not have their car get stolen.
That is a terrific PSA. Well done. I thought you were talking about a prostate exam when she said that's what I did. That's why I was all confused at the beginning when she gave her title and I'm, what do prostates have to do with anything? The show's insane.
No, it's just me. That feels like a challenge for next time I'm on. I have to make a prostate-related story. I'm not doing that, though. Carole, what's your story for us this week? Do you remember, of course you will remember, the old days when we used to talk about DOS attacks or denial of service attacks or distributed denial of service attacks. And this is typically when an unauthorized third party or a baddie pings a website over and over and over and over again, you know, effectively flooding the server so it can't deliver actual content to actual visitors. Yes Graham, I think you had a really great way of describing that back in the day, of 15 fat men going through a rotating door or something at once.
I think I changed it to hippopotamuses, because I didn't want to upset anyone who was large.
It was a very good explainer, though. That's perfect. So everything gets squeezed, and nothing gets in or out, and it's a big old mess. And there are a few better known DDoS attacks. Do you guys remember February 2020 attack reported by Amazon services AWS?
This was the attack on DIN the DNS service or something was it? No. No, DIN's another one, that was another one. Yeah, that was in 2016. No, this one was known because at its peak, this attack saw incoming traffic at the rate of 2.3 terabits per second. If you were to put badgers on top of each other, how high would that clump of badgers be?
That would probably be about similar.
Crystal clear, crystal clear, yes. Okay, I think now everyone understands that this is a big deal, is what you're saying.
And then you were mentioning the DIN attack. Do you remember it, Graham? Can you tell us about it?
It was a big DDoS attack against lots of websites. Wasn't it the one which exploited IoT devices? Yes.
Exactly. So the cameras, smart TVs, radios, printers, even baby monitors, they were compromised. And then these devices were all programmed to send requests to a single victim. So all the big sites got affected, Airbnb, Netflix, PayPal, Visa, Amazon, New York Times, Reddit, GitHub, on and on and on. And basically, these type of DDoS attacks at the heart is about rendering a website or service useless, which is the exact opposite of the attacks we see today, where someone's trying to sneak in and take loads of stuff away from you that you own, right? But there are occasionally motivations for taking down a website, right? What motivations come to mind if I told you that earlier this week, the royal family in the UK, their website was taken down.
Was it Harry and Meghan who did it? Was it them who attacked the royal family? Thom Hanks was probably in on it as well. Yeah, probably. Why would anyone be going to the Royal Family's website anyway?
Can you go there now? Yeah, okay, yeah. What do they have? I actually didn't even go and visit the website, which is outrageous. So it's royal.uk.
Royal.uk. Which I didn't even know. Nice URL. It's behind Cloudflare.
Cloudflare. Yeah, I just got that too. They must have turned that on.
Yeah, maybe they hit it real quick. Well, you can just turn it on if you're suffering an attack. That's true. So maybe they did that. Anyway, there's some lovely pictures there of the King and Queen Camilla.
Their website's very nice and responsive. Nice design. They put some money into this. Some press releases. So a state visit by the president of the Republic of Korea. Excellent. South Korea, I imagine. Excellent. Good, good. Keep that page. Keep that page. We're going to come back to that.
OK. There's a picture of President Macron and his old drama teacher there.
That's right. Kind of a terrifying photo of her. Anyway, so someone claimed responsibility for the attack, and they go by the name of Kill Milk. Does that ring any bells? Kill Milk? He reportedly heads up the Kill Net group, a group that seems has pretty close ties to Russian political agendas. So according to the Five Eyes Intelligent Network, that's agencies in Canada, Australia, New Zealand, US, UK, they warned last year that Killnet was one of several hacker groups that had pledged to support Russia and threatened to attack anyone who attacked Russia or supported Ukraine. These are the guys that attacked the Eurovision Song Contest last year. Do you remember that? Because they were in an attempt to stop Ukraine winning.
Oh, yeah. That day will go down in infamy.
So why would the royal family website, royal.uk, be taken down last Sunday morning? Turns out, just days after King Charles condemned the invasion of Ukraine, the site was taken down. See, King Charles, in what some are calling a wholly unprecedented move, dished some strong words speaking out against Russia's invasion of Ukraine during his landmark speech in the French Senate last Thursday morning. Mere days before the royal family's website was targeted.
Okay. How scandalous of him to have an opinion and to express it. He described the war as horrifying. King Charles also reported saying Ukraine must win its war and invoked the unity of Britain and de Gaulle's free French movement in the Second World War as an example of the need to stand together against unprovoked aggressions on our continent. Well, I think we need to modernize the royal family. And if what he said doesn't seem controversial to me, it seems quite legitimate. I mean, you would expect that the head of state to probably have that point of view regarding the war in Ukraine. I'd be more surprised if he went the other way. You were surprised that he had an opinion or that he expressed an opinion?
I was surprised that... No, of course I'm not surprised he has an opinion. I'm surprised that he vocalized it in the way that he did.
I guess it sets a precedent. And maybe we're going to hear more outpourings of opinions from Charles in the future about other countries too.
I'm reading his... I mean, maybe there was some other statement that he made, but I'm reading his speech and he mentions Ukraine in light passing. It's not like he went on and on about it, but he did enough to upset this Killnet group. So what a lame thing to do. It's not even like, okay yeah, you DDoS the website, good job. It's what, is it 1997 all over again? Big whoop. The upshot is the site was taken down for 90 minutes, displaying an error message on Sunday morning to those desperate to find out what people were up to on royal.uk, which would be the first place I would go on a Sunday morning. It's my homepage normally. And in a way, it's not a big deal, right? Buckingham Palace did the right thing. They got it back up and running. They told the world in a timely manner. I would have been more impressed if they'd hacked their social media. DDoSing a website? No. Hacking the social media? Okay. Does Prince Charles, or sorry, King Charles have social media?
Oh yeah, they're on Twitter and Instagram and all that stuff. I don't know if they're doing TikTok dances yet, but give it time.
They're not twerking? Oh jeez.
I think you're mixing them up with Fergie now. She's no longer a member of the royal family.
The royal family has 13.1 million followers on Instagram. Wow. More than Thom Hanks.
If your SIEM is causing an endless cycle of noisy alerts, manually writing generic detection rules, and limited data ingestion and retention, your SOC might need an upgrade. Well, Hunters is a SaaS platform purpose-built for your security operations team. With Hunters, you can ingest and normalize as much data as you have at a predictable cost without having to compromise on visibility and retention. Automatically cross-correlate data logs from your entire security and IT stack to connect and track events throughout your organization without switching screens. And leverage out-of-the-box and always up-to-date detections that cover 80% of security use cases. Solaris Group, a leading German fintech, implemented Hunter's SOC platform to eliminate the burden of redundant detection engineering and manual event correlation, allowing SOC analysts to focus on higher value tasks. Visit hunters.security to learn how your SOC can move beyond SIEM. That's hunters.security, and thanks to Hunters for supporting the show.
And we thank Devo for sponsoring the show. SOC analysts are often overworked and underappreciated. In fact, many consider leaving their jobs or changing careers altogether. Devo is hosting the third annual SOC Analyst Appreciation Day. This year's program includes presentations and discussions from some of the InfoSec community's most prolific thought leaders, including the likes of YouTube creator John Hammond, CISO Olivia Rose, and unpopular opinion guy Josh Copeland. This event will cover everything from real-life use cases to SOC automation, managing your mental well-being and more. You won't want to miss it. Join Devo and other cybersecurity industry professionals on October 18th, 2023 for sessions and panels focused on de-stressing, SOC career development and more. Visit smashingsecurity.com slash Devo to register. That's smashingsecurity.com slash Devo. If you work in security or IT and your company has Okta, this message is for you. For the past few years, the majority of data breaches and hacks you read about have something in common. It's employees. Hackers absolutely love exploiting vulnerable employee devices and credentials. But imagine a world where only secure devices can access your cloud apps. Here, credentials are useless to hackers, and you can manage every OS, even Linux, from a single dashboard. Best of all, you can get employees to fix their own device security issues without creating more work for IT. The good news is, you don't have to imagine this world. You can just start using Kolide. Kolide is a device trust solution for companies with Okta, and it makes sure that if a device is not trusted or secure, it can't log in to your cloud apps. Visit kolide.com slash smashing to watch a demo and see how it works. That's K-O-L-I-D-E dot com slash smashing. And welcome back. If you join us by our favourite part of the show, the part of the show that we like to call Pick of the Week. Pick of the Week. Pick of the Week. How can you? Isn't that Nora Ephron? Yeah, Nora Ephron. That's right. She did Harry Met Sally. We love that one. I love that this explains your Thom Hanks animosity. This is great. Came full circle.
Last week we were chatting about it, yes. A bunch of names were mentioned. And I was not one of them. And I felt sad, so. from the Zelda game? From the
new Zelda game, yeah. She's obsessed with that light dragon. And the light dragon glows, as the name might imply. There are lights. So I have been learning how to incorporate LEDs into costuming for this costume that I'm making. And this website I came across to buy the LEDs is called evandesigns.com. And it is very old school in a way that I love, and that it's a little niche part of the internet for hobbyists. And it's full of a lot of good hobbyist information, exactly what you need. How do I build this thing? Or if I'm trying to, I don't even know what I don't know. Can you please walk me through it? A top to bottom guide. Oh, wow. And it's very competently done. And it's meant for people who do hobby trains, train sets. But he's got a bunch of stuff for people who do costuming, and for someone like me who is, you know, I have a very basic understanding of circuitry, very basic, but even I was reading through this, I'm like, I can definitely handle making, you know, a string of LEDs, something like this, thanks to his help. So I'm just giving a shout out to that, evandesigns.com, because I really appreciate their help. Cool. We need pictures.
They've got some very cool looking stuff here. They've got for just $15, the equipment you can, I imagine put it on your car or maybe on your toy car to give it a Knight Rider style LED
I should do that on my car that would look amazing and if you want to light up your TARDIS they have a kit for that as well yes, yes they do and they have Geiger counter sounds and yeah, all sorts of stuff yeah, yeah, yeah So all your LED needs are at Evan Designs, but they also have a lot of resources on how to actually make the stuff work in the way you want it to, which is nice to see that people are still sharing that information. And it's not video. It's written. God bless it. I can just read it.
Beautiful. Crow, what's your pick of the week?
So mine's a book that I've experienced, right? I love a good whodunit. It's like someone described a whodunit as a book full of manners and intrigue, and I love that. That's kind of true. It's like your Sherlock Holmes kind of thing. And it's rare that you get a good one. So often they can just be a bit predictable, and maybe it's great for new readers to the genre, but if you've been around the detective block a lot, it's hard to be surprised. So my pick of the week is a book I'm enjoying called The Eight Detectives by Alex Pavesi. P-A-V-E-S-I. And I'll quote The Guardian here because they say it so well. So it is a set of seven Golden Age style mysteries where an abundance of brutal slayings in genteel surroundings are rendered in a heightened pastiche of the form. So in my terms, rollicking fun read. And it's surprising how the attacks transpire. There's this one scene where a victim is killed with a detachable tine from a fork. Oh. Right? Crazy. So all kinds of cute things. And even better, all of these short stories, these seven short stories, are nestled within a greater narrative where you have this fictitious author, Grant McAllister, and he's discussing his own set of detective rules for how you write a detective story with an editor. And this leads to the eighth murder mystery, which I'm getting to this evening. If it sounds like your thing, it's great. I'm enjoying it a lot. Eight Detectives, a novel by Alex Pavesi. And that is my pick of the week. No nitpicks.
Very good. Well done on no nitpick.
Nope. Not a single nitpick. Nope. Everything's perfect. Now, Carole, you've been having fun this week chatting to the guys from Devo. Yes, I spoke with Kayla Williams, Devo's very own CISO. And we talk about SOC Analyst Appreciation Day. This is where you'll be appreciated, guys. Listen up. Listeners, today on Smashing Security, I am chatting about all things SOC with security analytics platform Devo's very own CISO, or I should give the whole title, Chief Information Security Officer, Kayla Williams. Very warm welcome to you, Kayla. Thanks for coming on the show.
Thank you so much for having me. I'm really excited to be here. Cool. Now, Devo Technology is a cloud-native platform designed to defend all the nasty stuff out there. But more than that, the Devo team are the people behind the SOC Analyst Appreciation Day. Yeah, wow. Where to start? So I'm Kayla Williams. I have been the CISO here at Devo for a little over a year and a half now.
That is a really interesting background though to a CISO. I don't think I've heard anything similar. And I can see how those building blocks would help you be such a great asset, because you understand risk, you understand process, and you understand security. I wondered if you could help me understand the role of a security operations analyst, because we use this term SOC, right? SOC analysts. And just for some of our listeners, I know most of them totally know what this is, but there's going to be some of them that are going to really appreciate an explanation from you. What's in their day-to-day? What are they responsible for? SPEAKER_01. It's very much all the other roles in security. The SOC analyst role can vary depending on the organization or the industry that you're in. However, the day-to-day is really logging in and checking for any potential incidents or events that... Anomalies, if you will, that you're not expecting to see. And then investigating that, each company has their own risk that they're willing to take. You have to take risk just to have a company going, right? So every company is going to be a little bit different, but logging in to your SIEM, which I hope it's Devo, and seeing what's happening, what's been triaged or not triaged yet, and then doing your investigations. Unfortunately, there is a lot of monotony there, especially for the level one SOC analysts who come in. Typically, the ones that are moving into the field for the first time that are in school or have just graduated and want to get their hands dirty with security, you're going to be going through a lot of your alerts, looking to see for any potential indicators of compromise or IOCs and kicking off your own, I would call a mini investigation on your own before you escalated up your chain of command to say, okay, I've now identified something. And that, that I think is exciting when you identify something, it's not always great when you identify something, but for the individual, that's exciting. It's hey, I'm noticing something that's, this is an anomaly. This pattern isn't, it's not following patterns. There's maybe, maybe some user behavior that isn't expected. Or one of my favorites that I hear a lot about is the impossible traveler, Kayla logged into Boston. She lives in Boston. That makes sense. But all of a sudden, 20 minutes later, she's logging in from Alaska. You're spotting anomalies. It's almost needle in the haystack work. But when you find that needle, it can be really glorious for the person because you've done your job. SPEAKER_01. Exactly. And that gratification of actually finding something and then also helping your organization to reduce its risk. And that's really where I feel the SOC analyst is underappreciated, which will come into the day that Devo has to celebrate them. But this team, the SOC team is really your first line of defense. They're your eyes on glass. They are seeing things that it's coming in and out of your environment with precision and accuracy. And our mistakes made short, but mistakes are made in every role. Things do get by. But they're really the unsung heroes of your corporate defenses. And having those folks understand the business, understand what's normal, what's not normal, expected, unexpected, however you want to phrase it, really arms them with the knowledge to reduce your risk profile. They are essentially preventing financial loss, reputational risk, regulatory risk, obviously information security risk as well. The branding piece and the reputational risk is something that's often discounted. And that's where people say, oh, security is a cost center. Absolutely not. And maybe I'm the only one that feels that way. But no, security is not a cost center. They're saving your brand. They're saving your customers, saving face, if you will. The users are going, we're with you, Kayla. We agree. And when the renewals come up or when new prospects are asking about your defenses, that's your SOC. Number one is your SOC. And yes, we are a very expensive team to have, but balance that with your brand that you're protecting, whether it's a multi-million, billion-dollar brand, it's well worth the cost to keep that going. But ultimately, this isn't an easy job, though. SPEAKER_01. No, absolutely not. And because of coming into this role here and now having the SOC Analyst Appreciation Day, I'm very much aware of how little in the past where I've worked, it's been acknowledged because it is you're always on. There's always alerts, flooding of alerts, the monotony of having to go through them and make sure that they're, if they're false positive, marking them as that, opening an investigation, writing rule sets to make sure that, if you're seeing patterns that are all false positive, making sure that those are marked as such and removed from your processes. And it's just constant bombardment of noise. So tell me a little bit about the upcoming third annual SOC Analyst Appreciation Day. SPEAKER_01. So we are hosting it, SOCanalystDay.com. If you have not registered, it's October 18th, please do. Even if you are not in the SOC and you were just thinking about coming into security, it is a fantastic way to learn about the field. Because I think something that's often overlooked is people like, yeah, I want to get into security. There's a lot of jobs there. You have to be mentally tough to be in this field. I think we all deserve credit for that. The event is our third year. As you mentioned, from year one to year two, we nearly doubled the number of people that attended. So this year, we're hoping to have another record-breaking event. It is all online, but it is all day. So there you can come in, you can obviously being in a SOC, you probably have to have eyes on screen. You can listen to it in the background. You will hear my voice, unfortunately or fortunately. I don't know. You have a great radio voice. I think they're going to be in heaven. SPEAKER_01. But it's a wonderful event. This is my second year co-hosting it. I'll actually be in the studio recording all day. But I do have an event that I'm co-hosting, the full event all day, but moderating a panel for there's a seat for everyone in cyber that will touch upon what you and I just discussed a few moments ago around complementary skill sets and being able to transfer people in from other fields because that non-traditional background that I have has really opened up my eyes to how many other people could be in this field but maybe lack a cybersecurity degree or engineering background. And it's certainly a way to address some of the shortages that we're seeing across the board. Absolutely. And it also gives people out there that maybe are feeling stuck in a rut. Maybe you're in accountancy and you're thinking, this isn't for me. And you might find that cybersecurity desperately needs your risk assessing and your number crunching, right? We need all those skills. SPEAKER_01. I couldn't agree with you more. And I actually spoke at Blue Team Con in Chicago about a month ago on the non-traditional paths into security. And I did a segment on those complementary skill sets where I put them up on the screen and was drawing arrows between being an accountant and what kind of skill set that is. So having the attention to detail, being able to quickly analyze two sets of data and having the wherewithal to see those discrepancies that might be there, those patterns that have changed. And my favorite story is, and I talked about it at the event, a friend of mine hired a former bus driver as an incident response manager because this individual was used to having to write reports, being very detailed and also de-escalating situations. Another session that is extremely important to me is the mental health session that Peter will be running from CyberMinds. I had the pleasure of meeting Peter at RSA in a black hat. He came over from Australia, did his US launch back at RSA and CyberMinds is amazing. They have a program that is for cybersecurity professionals like all of us. And they come in and they teach you how to deal with stress because we have more stress than some people that were on the front lines during the pandemic and our day to day. And 77% of the survey respondents that Devo did with Wakefield Research have said that their stress levels at work directly affect their ability to keep customer data safe. They're making mistakes. They're not seeing things. They are so stressed out because they're so afraid they're going to make a mistake, that anxiety. And as someone who has anxiety and I talk about it openly, I do take anxiety medication. It is certainly a session that I highly encourage folks to attend that that's with cyber minds, one word with a Z at the end. And then, of course, John Hammond has SOC hacks. So John is on my television screen on my YouTube. Every time I turn it on, that's my husband's like, who is this guy? I'm like, oh, that's John. And this is free to attend, right? If anything ever sounded like a mental health day, this does because you're going to get all the love that you need. Now, if you guys want to register, this is where you go. Smashingsecurity.com slash Devo. That's D-E-V-O. So Smashingsecurity.com slash Devo. And is there anything else you'd like to add, Kayla, before we wrap up?
Thank you for coming on the show and for talking to us all. It's been amazing. And I think we're going to get lots of signups. Right, listeners?
Super stuff. And that just about wraps up the show for this week. Maria, I'm sure lots of our listeners would love to follow you online. What's the best way for folks to do that?
Well, if you want to hear my voice in your ear holes every day, I'm sure you do. Of course you do. Of course you do. My very own show, it is called T-Space Daily. We talk about space, all things space, space industry, commercial space, all the good stuff. And a little bit of space cybersecurity, too. So you find it wherever fine podcasts are purveyed or at space.n2k.com and I'm also at mvarmazis on Twitter and at varmazis on mastodon.social, mstdn.social.
Super duper. And you can still follow us on Twitter at smashinsecurity, no G, Twitter allows to have a G and we have a Mastodon account as well. Look for us up there. And don't forget to ensure you never miss another episode. Follow Smash Insecurity in your favourite podcast apps such as Apple Podcasts, Spotify and Overcast.
And huge, huge thank you to this episode's sponsors, Devo Hunters and Collide and of course to our wonderful Patreon community thanks to them all that this show is free for episode show notes, sponsorship info, guest list and the entire back catalogue of more than 341 episodes check out smashingsecurity.com
Until next time, cheerio, bye bye bye bye I feel like I might have given Thom Hanks a bit of a hard time. It was perhaps a little...
You definitely did. You did. You did. You think? You ate his guts.
I just... I did see one movie I liked Thom Hanks in. Well, other than Toy Story. Toy Story's all right. But...
You didn't like Castaway or anything?
I can't watch it because it's got Thom Hanks in it. I saw the movie...
That's a tautology, though. Yeah.
I saw the movie The Post, which I thought was really good. And it was only three quarters of the way through when I realised one of the actors was Thom Hanks. And I thought, oh, this is actually alright. So, maybe it's only when I recognised Thom Hanks that I've got a problem. Forrest Gump? Never watched it. It's got Thom Hanks in it. Yeah.




I would consider it an honor and privilege, but I would require to move.
A sleaze worthy of a royal family. It's a good thing they didn't ask for any additional money from the person to be hired! (Google translated.)